The recent Wikileaks dump allegedly revealed a database of CIA hacking tools that were developed to hack into mobile devices of every type.
The primary targets of these tools were Android and iOS devices and on the surface, it does seem like Android and iOS are chock full of security holes. The leaks reveal that everything from secure communication apps like Telegram and Signal to your mobile phone and smart TV is vulnerable.
Thankfully, it appears that the situation isn’t as dire as it first appears.
For one thing, both Alphabet (Google) and Apple have issued statements to the effect that most, if not all, of the vulnerabilities being highlighted have already been patched. Essentially, if your phone is up-to-date, as it should always be, you’re as safe as you can ever be. If you have been lax with updates, you need to worry.
Speaking to BGR , Will Strafach, a world famous iPhone hacker said that there’s nothing in the leaks to indicate that an up-to-date iPhone is vulnerable to anything. He also adds, “Android experts have said the same”, when referring to the Android vulnerabilities highlighted in the leaks.
“As we’ve reviewed the documents, we’re confident that security updates and protections in both Chrome and Android already shield users from many of these alleged vulnerabilities. Our analysis is ongoing and we will implement any further necessary protections,” says Heather Adkins, Google’s director of information security and privacy.
It’s also been pointed out that many of the hacks highlighted in this Wikileaks dump are publicly known vulnerabilities.
The point here isn’t that Wikileaks revealed that the CIA has hacking tools and that Android and iOS are vulnerable. Vulnerabilities are found all the time, and not just by the CIA, and they are patched all the time.
As far as vulnerabilities are concerned, it’s a constant race against time for both hackers and developers.
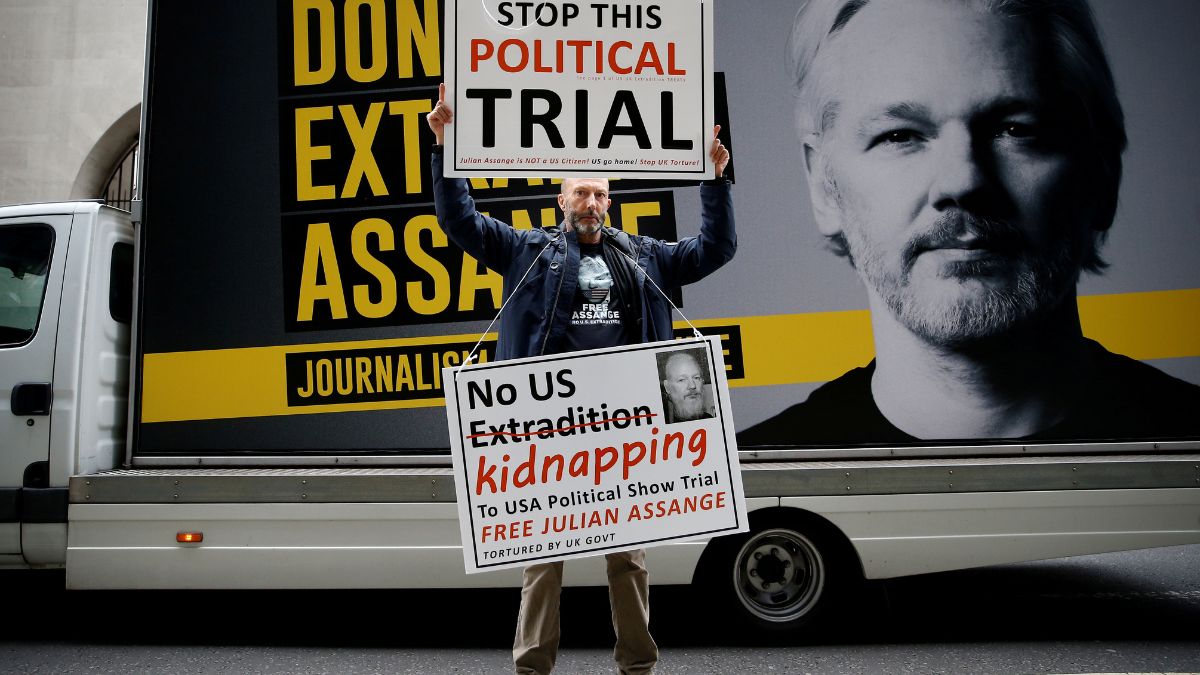
Even Wikileaks themselves have said that the purpose of the leaks was to “provoke a political and legal debate about the CIA’s cyber arsenal.” It’s not about the leaks.
Today, one can hardly call it surprising that the CIA and MI5 and the like have an arsenal of hacking tools at their disposal, it’s also very likely that they are actively working on hacks for the current generation of operating systems and that they will continue to do so in future.
If you really want to stay secure , keeping your devices up-to-date is the least you can do, but even that may not be enough.

)



)
)
)
)
)
)