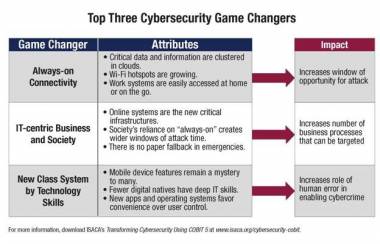
Cybercrime is on the rise, but will grow even faster if organisations ignore an emerging group of cyber security game changers: always-on connectivity, an increasingly IT-centric society, and a new class system that separates people by technology skills. ISACA’s latest guide, Transforming Cybersecurity Using COBIT 5, examines the impact of these game changers and how to manage and transform security by using COBIT 5, a business framework for the governance and management of enterprise information and technology. Along with publication of the guide, IT association ISACA also announced the formation of a global cyber security task force.
The three game changers named in the guide provide both motive and opportunity for cyber security breaches and criminal activities—especially the advanced persistent threat (APT) —if ignored:
“In just the past three years, the number of threats and vulnerabilities has grown almost exponentially. By using COBIT 5, security professionals have a systematic approach for overcoming some of their biggest internal barriers—especially inadequate budget and lack of senior management support,” said Rolf von Roessing, CISA, CISM, CGEIT, CISSP, FBCI, Lead Developer of The Guide and President of FORFA AG.
This latest addition to ISACA’s cyber security series is designed for information security managers, corporate security managers, end users, service providers, IT administrators and IT auditors. It includes guidance on using the COBIT 5 framework to integrate cyber security with an overall approach to security governance, risk management and compliance, as well as eight principles for transforming security.
“The enormous opportunities inherent with cloud, mobility, social networking and Big Data also create significant security risks, and most organisations are ill-prepared to respond effectively. If we want to defend ourselves from sophisticated and targeted cyber attacks, it’s time to shift the industry’s thinking from a focus on compliance and perimeter security to a more proactive posture that is all about protecting the crown jewels,” said Eddie Schwartz, CISA, CISM, chair of ISACA’s Cybersecurity Task Force and Chief Information Security Officer (CISO) at RSA, The Security Division of EMC.
A recent ISACA cybersecurity survey of more than 1,500 security professionals worldwide found that 94 percent of respondents believe that the APT represents a credible threat to national security and economic stability. Top risks were seen as loss of enterprise intellectual property (26 percent), loss of customer or employee personally identifiable information (24 percent) and damage to corporate reputation (21 percent).
ISACA Global Cyber security Task Force
As part of its ongoing commitment to helping business and IT leaders maximise value and manage risk related to information and technology, ISACA also announced the formation of a cyber security task force to drive research, guidance and advocacy. Eight information security professionals from locations around the world were named to the Cyber security Task Force:
Eddie Schwartz, CISO at RSA, The Security Division of EMC (USA) (chair)
Brent Conran, Chief Security Officer, McAfee (USA)
Marcus Sachs, Vice President for National Security Policy, Verizon (USA)
Neil Barlow, Head of Information Security Governance, Risk & Compliance (GRC), Euronext, NYSE (UK)
Samuel Linares, Director and Founder, Industrial Cyber security Center (Spain)
John Lyons, Chief Executive, International Cyber Security Protection Alliance (UK)
Manuel Aceves, Director General, Cerberian Consulting (Mexico)
Derek Grocke, Security & Infrastructure Manager, Internode (Australia)
“In recent past, global Cyber crime and related phenomena have grown exponentially with never-before-seen widespread losses and impact. The increasing number of targeted well-researched & sophisticated attacks on business and government entities is exposing their narrow and inconsistent approach to cyber security. ISACA’s latest Guide to Cyber security using COBIT 5 , identifies the key causative factors and provides a highly usable security governance roadmap that will help organisations in transforming their cyber security strategy and enable evolving an enterprise wide approach to security governance, risk management and compliance” said Vittal Raj, CISA, CISM, CGEIT,CRISC, CFE, CIA, CISSP, FCA and , International Vice President, ISACA.
“Formation of ISACA’s Global Cybersecurity Task Force is a step ahead to further educate the global security managers on the role of COBIT 5 and equip them better to tackle industry-wide cyber crime threats, ”said Avinash Kadam, CISA, CISM, CGEIT, CRISC, CISSP, CSSLP, GSEC, GCIH, CBCP, MBCI, PMP, CCSK, and Advisor to ISACA’s India Task Force.

)



)
)
)
)
)
)
)
)