A new kind of Android.Fakeapp malware discovered by Symantec researchers is targeting the Uber Android app and hacks into user data, allowing attackers to take over a user’s account. However, there is no need to panic straightaway as, reportedly, the malware is not widespread and most Uber users are currently unaffected. [caption id=“attachment_4209621” align=“alignleft” width=“380”] Representational image. Reuters[/caption] An Android.Fakeapp is a Trojan horse for devices running Android OS and it downloads “configuration files to display advertisements and collects information from the compromised device”. This particular Fakeapp, according to
Symantec, uses a replica of the Uber UI and keeps on popping up on the affected user’s device, asking them to input their Uber ID and password. After the user falls into the trap and enters their details, the information is transferred to a remote server. To make the process appear more legitimate, the screen shown after the next button is pressed is from the real Uber app, which displays the user’s current location. [caption id=“attachment_4288177” align=“alignnone” width=“607”]
Fake Uber app screens for users to enter their registered mobile number and password. Symantec[/caption] This screen is obtained from a deep link URL to the Uber app, which in turn gets hold of the victim’s location and the pickup point. Deep linking takes the users to specific content within an app via a URL. [caption id=“attachment_4288181” align=“alignnone” width=“300”]
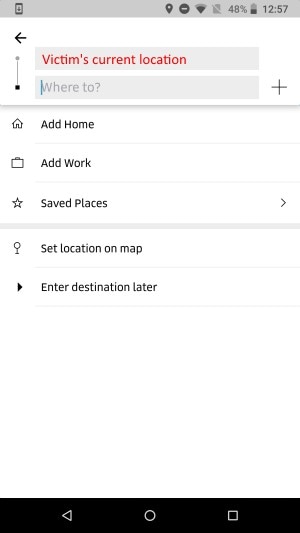 Screen of the legitimate app showing the user’s current location. Symantec[/caption] However, as we mentioned earlier, most users needn’t worry. A Gizmodo
report claims that this fakeapp is not available on the Play Store and that users would have to download it from an external source. “Users are likely in Russian-speaking countries in limited number. We don’t anticipate such an app to be in wide-scale distribution,” a Symantec spokesperson said, according to the report.
Screen of the legitimate app showing the user’s current location. Symantec[/caption] However, as we mentioned earlier, most users needn’t worry. A Gizmodo
report claims that this fakeapp is not available on the Play Store and that users would have to download it from an external source. “Users are likely in Russian-speaking countries in limited number. We don’t anticipate such an app to be in wide-scale distribution,” a Symantec spokesperson said, according to the report.
However, there is no need to panic straightaway as, reportedly, the malware is not widespread and most Uber users are currently unaffected.
Advertisement
End of Article


)
)
)
)
)
)
)
)
)



