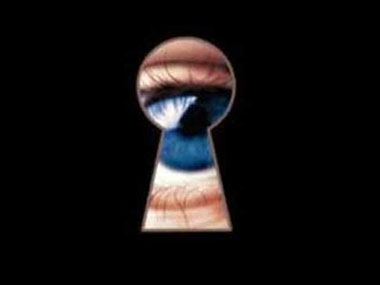
Millions of unsuspecting users could be exposing themselves to privacy risks simply by reading emails. This is because of a proliferation of email trackers that use a tiny, invisible pixel served from a third party site, and embedded through HTML in the email. The single pixel tracker can be used to find out when an email has been read, the location where the email was accessed, and the device with which the email has been read. [caption id=“attachment_4263803” align=“alignleft” width=“380”]  Getty Images[/caption] The email tracking services are sold as marketing services and can use multiple social media platforms and ad delivery networks. For example, Mail Chimp, a marketing automation platform can be used to run marketing campaigns on Facebook and Instagram to direct users to a website, then use re-marketing ads by Google to drive sales. SendGrid provides real-time analytics on geography, time, ISP and device type for marketing emails. Drip connects to a number of applications and services and allows for email campaigns as well as triggers for sending one off emails depending on the actions of a potential customer. Mailgun allows for advanced tracking, allowing marketers to figure out which consumers provide the best returns, depending on device, timing and email provider. MailTrack is a Chrome extension allows you to know when your emails have been opened in real-time, and Streak can be installed into your Gmail account. A reporter for Wired used Streak to find out when his emails to Apple were opened while setting up interviews for writing a book on the iPhone. He had been sending emails but they were not being replied to, so the reporter used the tracker to check if his emails were even being read. Through the tracking service, he found out that not only were his emails being read but were being circulated within the company. A tracker on a mail sent to Tim Cook revealed that the email was accessed on a desktop computer with Microsoft Windows as the operating system. Tracking his friends and family revealed the potential privacy problems of the trackers, which allowed him to snoop on the location and activities of his contacts, as well as find out how many people read his emails. The trackers use multiple approaches to gain information from the users. The trackers can be embedded in colours, fonts, invisible pixels, or hyperlinks. Deep links to applications such as Amazon or Facebook allows the related apps to be fired up in the background on a smartphone, through which the companies can gain additional information about the user depending on the application permissions. Facebook can use IP-based tracking to find out the location of the user through the email, even if the user has not granted the permission to the Facebook application for tracking the location. The problem becomes exacerbated when the trackers are used maliciously. For example, the trackers can find out the habits of the person by checking when the email has been read, the device being used, as well as the location through the IP address. If an individual is visiting another city, the trackers can be used to identify the hotel in which a sent mail is opened. The trackers are thus a threat to physical security as well. Email users interested in protecting their emails from sending read receipts, and tracking of other data, can do so through PixelBlock, a Chrome extension that prevents pixel-based tracking, and displays a red eye next to the email when a tracker is identified, or Ugly Email, a Gmail extension that blocks more than 22 known trackers.
The email tracking services are sold as marketing services, and can use multiple social media platforms and ad delivery networks.
Advertisement
End of Article


)
)
)
)
)
)
)
)
)



