The
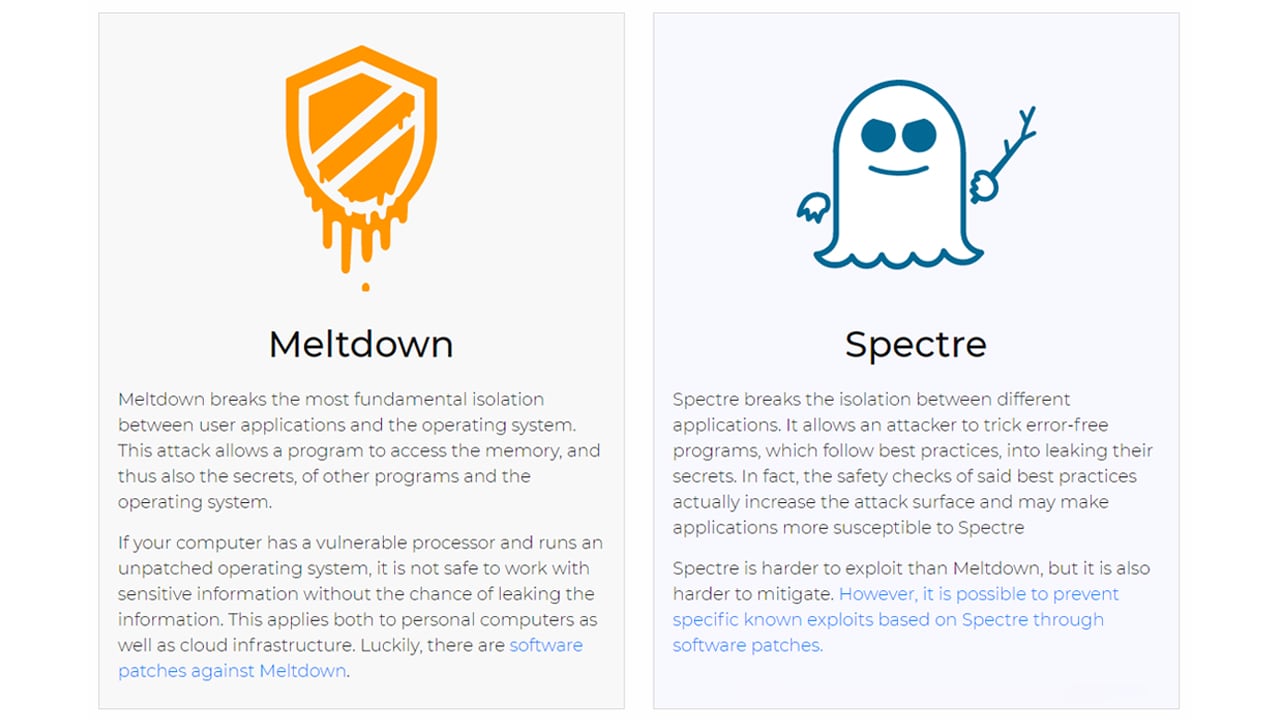
Meltdown and Spectre vulnerabilities were discovered last year, but only disclosed recently to the public. Both vulnerabilities are so fundamental to CPU design that around 20-years’ worth of processors are already affected and upcoming designs cannot be totally secure. To eliminate these vulnerabilities entirely will require a rethink of how a modern processor functions. At the heart of the vulnerability is a modern processing technique known as speculative execution. In other words, this technique involves the computer performing a task before it’s needed. Speculative execution went mainstream between 15 and 20 years ago, so theoretically, every CPU made in the last 20 years or so is vulnerable. What’s at stake here? [caption id=“attachment_4290551” align=“alignleft” width=“380”] Spectre will haunt us for years[/caption] To understand this, we first need to understand a little bit about how a computer handles data. Say you’re using the Chrome browser. You drop by Amazon and buy something, check your mail, Facebook, etc. These actions require you to type out passwords, payment information, etc. and you do this with the assumption that the data is securely transmitted. The catch here is that while the transmission is secure, every single keystroke of yours will have to pass through the processor of your computer before it is secured. This data is stored in something called cache memory, usually on your processor itself. It’s extremely sensitive data and clearly, must not be allowed to fall into the wrong hands. A modern processor (Intel, AMD, ARM, etc.) and operating system (macOS, Windows, Android, etc.) will very effectively isolate the memory for each program. Your data in Chrome will simply not be accessible to an outside program and vice versa. An operating system also stores data in the cache. The security of this OS data is even more important to secure as it can literally hold the keys to your computer. Now here comes the complicated bit. When a computer processor (CPU) performs speculative execution, changes to the processor state can be detected and theoretically used to determine the location of secure data and steal it. In the case of Meltdown, it gets worse, but more on that later. If this all seems like gibberish, don’t worry. Simply continue reading and all will be clear soon enough. [caption id=“attachment_4290431” align=“alignnone” width=“1280”]
 Spectre and Meltdown are the same family of vulnerability and effect just about every processor made in the last 20 years[/caption] Effectively, a malicious program will be able to read all that sensitive information. Your passwords, encryption keys and more can potentially be stolen. For cloud computing providers like Amazon and Microsoft, this is a very serious vulnerability. Cloud computing usually involves
virtualisation, i.e, virtual computers that share the same computer hardware. As an example, if you have a 10-core CPU with 16 GB RAM, you can create two virtual PCs using 4 cores and 8 GB of RAM each. There’s a great deal of flexibility. [caption id=“attachment_4290439” align=“alignnone” width=“640”]
Spectre and Meltdown are the same family of vulnerability and effect just about every processor made in the last 20 years[/caption] Effectively, a malicious program will be able to read all that sensitive information. Your passwords, encryption keys and more can potentially be stolen. For cloud computing providers like Amazon and Microsoft, this is a very serious vulnerability. Cloud computing usually involves
virtualisation, i.e, virtual computers that share the same computer hardware. As an example, if you have a 10-core CPU with 16 GB RAM, you can create two virtual PCs using 4 cores and 8 GB of RAM each. There’s a great deal of flexibility. [caption id=“attachment_4290439” align=“alignnone” width=“640”] Virtualisation is the backbone of cloud computing, and spectre undermines it.[/caption] These virtual PCs are normally secure and completely isolated from each other. One can be running Linux while the other Windows, it doesn’t matter. To a user, they behave like a real computer. This is useful in cloud computing as every task or user can be allotted just as many resources as needed for that particular task or user. It’s simply more efficient. Since Spectre exploits can, in theory, steal any data from a processor, they can also, in theory, steal any data from any virtual computer running on that shared hardware. If PayPal, Amazon.com and a malicious website are by some chance running on shared hardware as separate virtual instances, that malicious site could theoretically steal sensitive data from the other, perfectly secure and legitimate service. If the flaw is 20-years old, why wasn’t it discovered sooner? CPUs are extremely complex structures and finding every single vulnerability in a particular design might very well take decades. Also, the CPUs were found to be vulnerable to so called
side-channel attacks. A side-channel attack is one that relates to the “physical implementation of a computer system” rather than an inherent weakness in design. Information like power consumption or sound can be sources of information. How does one defend or even test for something like that? It’s certainly not easy.
Think of it as a player’s tell in a poker game. While the player’s face might be expressionless, and their cards hidden, giveaways like a twitching eyelid can be clues as to what that player is thinking. Once you find a tell, you can exploit it. The same analogy applies to Spectre and Meltdown. What is Meltdown and can it be fixed? Meltdown is a vulnerability that breaks the isolation between apps and the OS. It primarily affects Intel and Apple chips and also ARM’s upcoming Cortex A75 chip. The A75 will make its way into 2018’s flagship mobile chipsets, including Samsung’s Exynos and Qualcomm’s Snapdragon. [caption id=“attachment_4290465” align=“alignnone” width=“640”] Intel CPUs are worst affected by the vulnerability[/caption] AMD chips are unaffected. Thankfully, this vulnerability is easy to fix. The bad news is that the fix can impact the performance of a computer. Patches for Meltdown have already been issued for all major platforms. Updates are also coming out to other platforms. What is Spectre and can it be fixed? Spectre is a more widespread issue that breaks the isolation between programs. It basically affects every CPU made in the last two decades, including those from AMD and even IBM. On the plus side, Spectre is also very hard to exploit. [caption id=“attachment_4290475” align=“alignnone” width=“640”]
 Spectre will haunt chipmakers and researchers for years to come[/caption] Think of it this way, if your PC were a ship, knowing that Spectre exists is like knowing that your ship is leaky. The only problem is that you don’t know how it’s taking on water. You patch up the holes you find, but it may still be impossible to find all the holes on the ship. The only solution for perfectly securing yourself is to build a new ship with entirely new construction techniques. In other words, CPUs might have to be redesigned from the ground up. The major stakeholders have already issued updates and patches for known Spectre vulnerabilities. As and when new vulnerabilities pop up, they will need to be fixed as well. Am I safe? Borrowing a phrase from the seminal Hitchhiker’s Guide to the Galaxy, Don’t Panic! [caption id=“attachment_4290477” align=“alignnone” width=“1280”]
Spectre will haunt chipmakers and researchers for years to come[/caption] Think of it this way, if your PC were a ship, knowing that Spectre exists is like knowing that your ship is leaky. The only problem is that you don’t know how it’s taking on water. You patch up the holes you find, but it may still be impossible to find all the holes on the ship. The only solution for perfectly securing yourself is to build a new ship with entirely new construction techniques. In other words, CPUs might have to be redesigned from the ground up. The major stakeholders have already issued updates and patches for known Spectre vulnerabilities. As and when new vulnerabilities pop up, they will need to be fixed as well. Am I safe? Borrowing a phrase from the seminal Hitchhiker’s Guide to the Galaxy, Don’t Panic! [caption id=“attachment_4290477” align=“alignnone” width=“1280”] The most useful instruction ever. Image:
nslm/Wikimedia Commons[/caption] These vulnerabilities are incredibly hard to exploit and there is no known attack involving these vulnerabilities. It is possible that attacks will eventually be developed, but that hasn’t happened yet. Also, as long as you ensure that all your devices and programs are up to date, you can’t get any safer than you already are. How do I protect myself? It’s simple: Don’t turn off your updates. Microsoft
rolled out an update to Windows 10 that protects against Meltdown. Apple’s macOS, iOS and tvOS devices have
already received some fixes, more are on the way. Users of older versions of Windows, including the now unsupported Windows 7 will also receive the update soon. Linux users will also have received updates, with more on the way. [caption id=“attachment_4290499” align=“alignnone” width=“872”]
The most useful instruction ever. Image:
nslm/Wikimedia Commons[/caption] These vulnerabilities are incredibly hard to exploit and there is no known attack involving these vulnerabilities. It is possible that attacks will eventually be developed, but that hasn’t happened yet. Also, as long as you ensure that all your devices and programs are up to date, you can’t get any safer than you already are. How do I protect myself? It’s simple: Don’t turn off your updates. Microsoft
rolled out an update to Windows 10 that protects against Meltdown. Apple’s macOS, iOS and tvOS devices have
already received some fixes, more are on the way. Users of older versions of Windows, including the now unsupported Windows 7 will also receive the update soon. Linux users will also have received updates, with more on the way. [caption id=“attachment_4290499” align=“alignnone” width=“872”] Make sure that all your software is updated regularly.
Image: osde8Info/Flikr[/caption]
Google has issued a fix as part of its December 2017 security patch for Android devices. These patches will need to be sent out to your device via your device manufacturer. Supported Pixel and Nexus devices will have already received the update. ChromeOS has also received the update. All your browsers, including Google Chrome, Firefox, Edge and Safari are getting updates soon. Make sure automatic updates are enabled for them. This should be on by default anyway. The major cloud computing services have already been updated and clients are being informed of the additional steps that they need to take to protect their data. Users of AMD CPUs need not worry too much as the more serious exploits don’t work on those chips. Smart devices like the Google Home and Chromecast are currently unaffected. If automatic updates are on, you don’t need to worry. How slow will my PC get? The average user will not notice a difference, Certain specialised services and workloads may get affected, however. Early reports suggested that the performance impact of the Meltdown patch for Intel systems could be as bad as 50 percent. Thankfully, that doesn’t seem to be the case.
A report on TechSpot has shown that the update to Windows 10 hasn’t had any notable performance impact on the performance of your PC if it’s running the latest hardware. TechSpot does note that certain disk speed tests slowed down by half, however. The impact on older hardware is unknown at this time. Google, Amazon and Microsoft have confirmed that the
impact of the update to their servers has been negligible. AMD PCs aren’t affected. The impact on mobile devices running also appears to be insignificant. What is speculative execution? [caption id=“attachment_4290535” align=“alignnone” width=“1280”]
Of course it’s confusing! CPUs are infinitely complex structures.[/caption] Consider the following example. Say your processor can only add two numbers at a time and you need to perform a calculation like 2+4+6+8+10+12. A processor without speculative execution will perform the calculation in the following manner: 1. Add 2 and 4: 2+4=6 2. Store the sum of 2 and 4, which is 6, to memory. 3. Recall the sum of 2 and 4 from memory and add it to the next number in the calculation. 4-12. Store that number in memory and repeat for each number in the calculation. Each of these steps consumes time and resources. With speculative execution, a computer might use spare resources to add 6 and 8 as well as 10 and 12 separately and store their values. Thus, the speculative process would now look something like this: 1. Calculate 2+4, 6+8 and 10+12 2. Store the values of the three sums. 3-6. Add the values of the previous calculations in order. This is a vastly oversimplified view that will probably give heart attacks to any chip designer or programmer reading this, but it should at least give you an idea of how much time speculative execution can potentially save. In this oversimplified example alone, efficiency is doubled. It’s also possible that that the speculatively executed code is not needed, wasting those processor cycles. More often than not, however, that code is needed, making this technique a critical component for processor efficiency. The actual process is extremely complicated and involve a whole family of predictive algorithms that are way beyond the scope of even an average computer engineer to explain. For more details on Meltdown and Spectre, head here.


)
)
)
)
)
)
)
)
)



