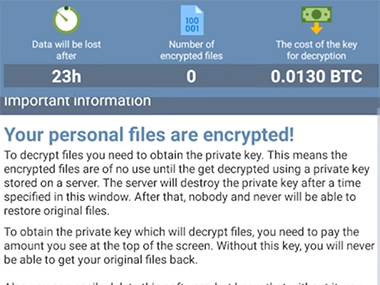
The Indian Computer Emergency Response Team (CERT-In) has issued a medium severity alert on the DoubleLocker ransomware which affects Android devices. The malware spreads through a fake Adobe Flash downloader and then persists on the system by replacing the default home button functionality, and is triggered when the user taps on the home button. The malware then encrypts all the data on the smartphone and changes the PIN of the device. [caption id=“attachment_4179463” align=“alignleft” width=“380”]  Image: ESET,[/caption] This is the first malware in the wild that encrypts the data as well as replaces the SIM. The user cannot access the device after the malware is activated. A 0.013 bitcoin payment is demanded within a narrow window of 24 hours, after which the user permanently loses access to their data. The only way to recover the device from an infection is to factory reset the smartphone. The files on the device are encrypted using the AES encryption algorithm. Security researchers from **ESET discovered the malware** . CERT-In advises users to download applications from only trusted stores, regularly backing up all the data on Android devices, review permissions of an applications before installation, installing an updated anti-virus solution on the device, and to keep the OS patched with the latest security updates. CERT-In also advises users to refer to the best practices ( PDF) for smartphones.
The malware encrypts all the data on the smartphone, changes the PIN of the device, and demands a bitcoin payment for decryption of the files.
Advertisement
End of Article


)
)
)
)
)
)
)
)
)



